Securing Operational Technology (OT)

The need to secure information is likely not a new topic for most manufacturers. Security controls around Information Technology (IT) are already in place in many companies, particularly public and large private companies.
But, what about Operational Technology (OT) security? Awareness about the need to protect the full extent of manufacturing machines and processes is still not as high as with IT security.
This topic is apparently now on the radar of both the US and UE governments, judging by the multiple reports released over the past few months that highlight supply chain security risks and directions. One of the most recent publications, a draft of Special Publication 800-82, provides a framework for securing operational technology (OT) within the US defense contractor network. Issued this past April, it sheds some light on the Department of Defense Cybersecurity Maturity Model (CMMC) program, which seeks to improve information security within the US defense contractor network. CMMC 2.0 includes a requirement for manufacturers to secure their OT.
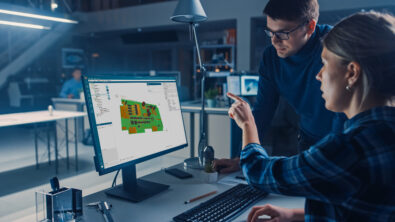
What does that mean for electronics manufacturers? How can you meet increasing OT security requirements when your production line includes old, but critical, machines that run on correspondently old operating systems?
According to Zac Elliot, Technical Marketing Engineer at Siemens, meeting the new CMMC requirements might not be as onerous as it sounds. In his most recent column published a few days ago by iConnect, Zac reviews the recent EU and US publications on intellectual property security in the supply chain, and homes in on the CMMC requirements. He also explains how the typical PCB assembly process is already set up to support manufacturers in ensuring the integrity of the components they use, leveraging the automatic optical inspection (AOI) integrated in SMT machines.