Internet of Things Product Development the Right Way
The Internet of Things (IoT) has great potential for business workers and consumers, but there is a lot of confusion about the IoT infrastructure and connected devices receiving connectivity.
In a simplistic high-level breakdown, IoT is an ecosystem that allows hardware and objects we interact with everyday to have network connectivity – able to communicate directly with one another. By 2020, there will be at least 26 billion connected “Things,” according to the Gartner research analyst group.
What is This IoT Madness?
If implemented properly, just about any person, object, or animal will be able to transfer data using an assigned IP address – so a medical patient with an implanted heart monitor, for example, can transfer data to a doctor, or farmers will be able to pull information from livestock.
IoT presents great benefits, but trying to keep things and networks secure is a constant headache. Billions of things transporting data, including personal and corporate information, and sharing it between physical servers, cloud computing resources, and end-user products creates gaps in security that are posing significant challenges.
Here is what Ganesh Ramamoorthy, Research Vice Principal at Gartner, recently noted (via press release):
“Governance management and operations of security functions will need to be significant to accommodate expanded responsibilities, similar to the ways that bring your own device (BYOD), mobile and cloud computing delivery have required changes – but on a much larger scale and in greater breadth. IT will learn much from its operational technology (OT) predecessors in handling this new environment.”
By the end of 2017, over 20 percent of enterprises are expected to have digital security services dedicated to keeping business initiatives and IoT services secure, according to the Gartner research analyst group. However, companies may not realize some of the effective tools they could take advantage of while creating new IoT solutions.
Available Solutions
 The need for both application lifecycle management (ALM) and product lifecycle management (PLM) platforms operating in a cohesive ecosystem will help prop up IoT. Growing software needs for connected Things will help drive interest in ALM-PLM integration, as PLM on its own doesn’t sufficiently cover development needs.
The need for both application lifecycle management (ALM) and product lifecycle management (PLM) platforms operating in a cohesive ecosystem will help prop up IoT. Growing software needs for connected Things will help drive interest in ALM-PLM integration, as PLM on its own doesn’t sufficiently cover development needs.
Looking ahead, software will play an even more critical role in consumer and B2B products we use every day, so verifying stability in the IoT landscape becomes a necessity.
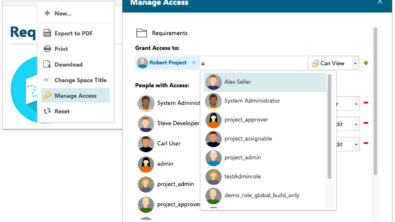
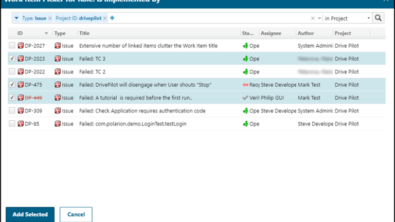
Proper ALM and PLM are needed if a company is developing a product that heavily relies on software, and having both platforms integrated helps provide the following support: PLM tool sets are unable to manage software development, and ALM tool sets are unable to manage product development. ALM-PLM integration aids in identifying – and resolving – problems that would not be detected while simply looking at software or hardware. ALM-PLM governance helps better analyze both hardware-in-the-loop and software-in-the-loop testing during your development lifecycles, further legitimizing your internal assets ahead of final product launches.
Final Thoughts
This sudden adoption of IoT, with companies scrambling to create new connected solutions, will only open the door to significant cybersecurity issues. Software developers and development teams must have suitable tools and processes available to them – and using Polarion Software application lifecycle management (ALM) will help fill the void, but don’t forget about the importance of proper integration with PLM tools.
To learn more, download our free whitepaper: