Article Roundup: Embedded Device Security, EV Battery Design, UVM 1800.2, Outlier Bugs & Smart City Mobility
- Device security: when ‘how’ becomes just as important as ‘what’
- Improve EV Battery Pack Designs With CAD-Embedded Thermal Simulation
- Updated UVM Cookbook Supports IEEE 1800.2 Standard And Emulation
- When Bugs Escape
- Smart Cities’ Head Start On The Mobility Future
Device security: when ‘how’ becomes just as important as ‘what’
Embedded.com
 Embedded device security has become a central concern of many industries, including automotive, medical, and industrial. For many developers, enhancing device security ends at incorporating security features, such as encryption, or conducting software security analysis. This, however, cannot address the attacks that devices will endure in the future, attacks that do not exist today. To that end, this article presents techniques for making devices difficult to exploit once infiltrated.
Embedded device security has become a central concern of many industries, including automotive, medical, and industrial. For many developers, enhancing device security ends at incorporating security features, such as encryption, or conducting software security analysis. This, however, cannot address the attacks that devices will endure in the future, attacks that do not exist today. To that end, this article presents techniques for making devices difficult to exploit once infiltrated.
Improve EV Battery Pack Designs With CAD-Embedded Thermal Simulation
Power Electronics World
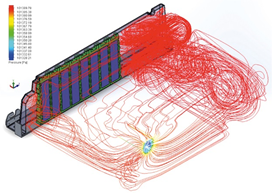 The challenges of electric powertrain engineering focus on the price and size of the battery pack, electric motor efficiency, and the balance between drive range, performance, and driver experience features. The thermal behavior of the battery, motor, and other electronics is critical to this balance, as excess heat wastes energy and causes malfunctions. Advanced CFD tools enable automotive designers to investigate and optimize designs during prototyping, reducing development time and cost by up to sixty percent.
The challenges of electric powertrain engineering focus on the price and size of the battery pack, electric motor efficiency, and the balance between drive range, performance, and driver experience features. The thermal behavior of the battery, motor, and other electronics is critical to this balance, as excess heat wastes energy and causes malfunctions. Advanced CFD tools enable automotive designers to investigate and optimize designs during prototyping, reducing development time and cost by up to sixty percent.
Updated UVM Cookbook Supports IEEE 1800.2 Standard And Emulation
SemiEngineering
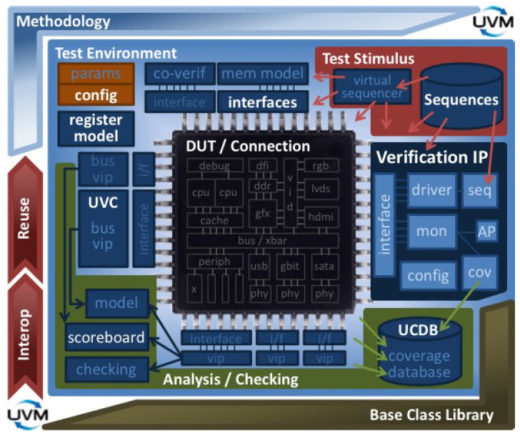 The Universal Verification Methodology (UVM) is a standard library of SystemVerilog classes that supports a modular and reusable testbench architecture for constrained-random functional verification. With the adoption of UVM as IEEE 1800.2 and increasing demand for emulation, Mentor’s UVM Cookbook has been fully updated to reflect the new standard and to support emulation. The Cookbook provides downloadable examples and how-tos in an online, searchable format to help users take full advantage of UVM.
The Universal Verification Methodology (UVM) is a standard library of SystemVerilog classes that supports a modular and reusable testbench architecture for constrained-random functional verification. With the adoption of UVM as IEEE 1800.2 and increasing demand for emulation, Mentor’s UVM Cookbook has been fully updated to reflect the new standard and to support emulation. The Cookbook provides downloadable examples and how-tos in an online, searchable format to help users take full advantage of UVM.
When Bugs Escape
SemiEngineering
Outlier bugs in SoC designs are flaws that can only be exposed by exercising the design outside its normal flow or operating parameters. These bugs require an incredibly complex sequence of scenarios to be exposed, meaning they are often discovered late in the verification cycle. Formal verification and portable stimulus can help to discover outlier bugs, but experts believe that a more fundamental change to verification methodologies will be needed to completely remove outlier bugs.
Smart Cities’ Head Start On The Mobility Future
SemiEngineering
 While autonomous vehicles are still in early developmental stages, connected cars and smart city infrastructure are arriving today with significant upside for safety, traffic, and navigation. For example, vehicle to infrastructure (V2I) connectivity is helping reduce travel time by forty percent in some of Seattle’s most congested corridors with reactive traffic signals and management software. These capabilities are only expected to become more powerful as more cars are connected to city networks, and human and AI pilots alike can communicate with increasing speed and effectiveness.
While autonomous vehicles are still in early developmental stages, connected cars and smart city infrastructure are arriving today with significant upside for safety, traffic, and navigation. For example, vehicle to infrastructure (V2I) connectivity is helping reduce travel time by forty percent in some of Seattle’s most congested corridors with reactive traffic signals and management software. These capabilities are only expected to become more powerful as more cars are connected to city networks, and human and AI pilots alike can communicate with increasing speed and effectiveness.