Expert Updates: CPUs+FPGAs, Hierarchical DFT, Microsoft Azure for IoT, Cloned Electronics, Co-Emulation
- IoT in the Cloud with Microsoft and Mentor
- Supporting CPUs Plus FPGAs – Part 1, Part 2, Part 3
- Writing Co-Emulation Testbenches, Transactors
- Drawing on Hierarchical DFT to Benefit All Designs and Flows
- Invasion of the Hardware Snatchers: Cloned Electronics Pollute the Market
IoT in the Cloud with Microsoft and Mentor
SemiWiki
 Mentor has joined Microsoft Azure Certified for the Internet of Things (IoT). The integration brings the IoT community support for both gateway and edge device configurations, pre-integration and testing with Microsoft Azure SDKs, embedded and cloud services, and security.
Mentor has joined Microsoft Azure Certified for the Internet of Things (IoT). The integration brings the IoT community support for both gateway and edge device configurations, pre-integration and testing with Microsoft Azure SDKs, embedded and cloud services, and security.
Supporting CPUs Plus FPGAs – Part 1, Part 2, Part 3
Semiconductor Engineering
Pairing a CPU and FPGA has been possible for quite some time, but two things have changed recently. First, the industry has reduced the latency of the connection between them and second, we now appear to have the killer app, convolutional neural networks, for cloud databases. In this three-part series industry experts, including our own Ellie Burns and Gordon Allan, discuss these changes and the state of the tool chain to support this combination.
Part 1: What the toolchain looks like today and the different mindsets within those flows.
Part 2: Who is the real user and how will they program this type of solution?
Part 3: Partitioning, security issues, verification and field upgradeability.
Writing Co-Emulation Testbenches, Transactors
EDN Asia
 By adopting co-emulation for testbench acceleration, design teams can move their verification strategy up a level of abstraction, and achieve the verification performance and productivity necessary to fully debug and develop the most complex electronic hardware and software-based systems.
By adopting co-emulation for testbench acceleration, design teams can move their verification strategy up a level of abstraction, and achieve the verification performance and productivity necessary to fully debug and develop the most complex electronic hardware and software-based systems.
Drawing on Hierarchical DFT to Benefit All Designs and Flows
Tech Design Forum
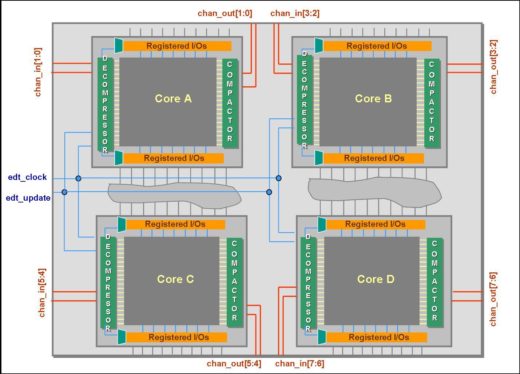 The hierarchical DFT idea of divide-and-conquer for DFT insertion and test generation is extremely valuable for large designs. With hierarchical DFT, pattern generation is performed concurrently on the blocks early in the design phase as soon as each block is ready.
The hierarchical DFT idea of divide-and-conquer for DFT insertion and test generation is extremely valuable for large designs. With hierarchical DFT, pattern generation is performed concurrently on the blocks early in the design phase as soon as each block is ready.
Invasion of the Hardware Snatchers: Cloned Electronics Pollute the Market
IEEE Spectrum
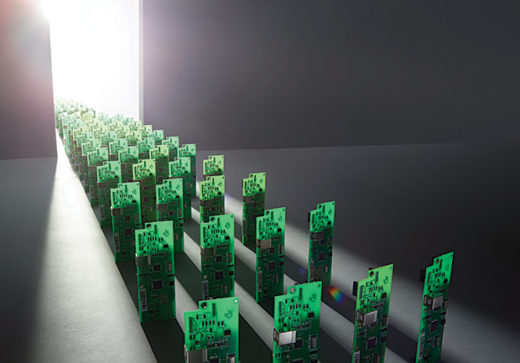 Contrary to counterfeit electronics of the past, modern cloned electronics are made from their own components, boards, and systems from scratch and then packaged into superficially similar products. The clones may be less reliable than the genuine product, but may also host unwanted or malicious software, firmware, or hardware. Buyers may not know the difference, or even know what to look for.
Contrary to counterfeit electronics of the past, modern cloned electronics are made from their own components, boards, and systems from scratch and then packaged into superficially similar products. The clones may be less reliable than the genuine product, but may also host unwanted or malicious software, firmware, or hardware. Buyers may not know the difference, or even know what to look for.
