Employing a Hierarchical Methodology for SoC Testing
When faced with a complex problem, engineers often employ a divide and conquer approach to efficiently come up with a solution. They break up a problem into sub-problems of the same type, solve these sub-problems, and then combine the results at the top level. They develop a hierarchy. Complex System on a Chip (SoC) designs are no exception…
These designs are built using a hierarchical structure of cores that tackle specific functionality, which together form the overall system. So, it is no wonder that test engineers employ a hierarchical DFT methodology for SoCs. Why? Because the SoC is already hierarchical and they do not have the time and compute resources to run a flow that includes analyzing all the SoC DFT structures and patterns at once.
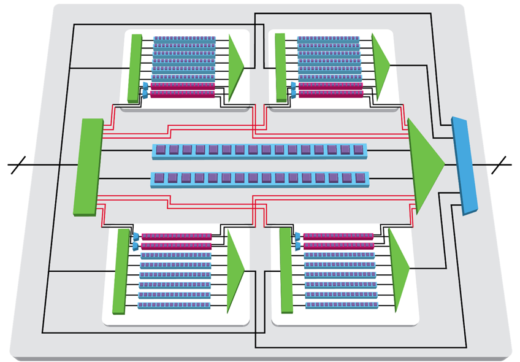
The Tessent team has developed an RTL-based hierarchical DFT methodology that includes inserting all DFT (including BIST for memory and logic) at the core level and the generation and verification of test patterns either for a single core or a group of cores. The core or a group of cores is the least common denominator in a hierarchical flow and it is the lowest hierarchical level at which test patterns are applied.
In order to effectively segment the design so that hierarchical DFT can be performed at lower core levels, each core (or group of cores) must be properly isolated. Two key components of core isolation are:
- Core-level clocking: placing clock control logic inside the core that is programmable by scan data. This is easily achievable by inserting on-chip clock controllers (OCCs) into the core with Tessent ScanPro, which has the benefit of automated setup and test procedure creation during ATPG.
- Wrapper chains: provide guaranteed control for all inputs of a core and guaranteed observation of the outputs. As long as you can access the wrapper chain, you can test that core without compromising test coverage. When testing the contents of the core, otherwise known as Internal mode, the wrapper chains are configured to launch values into the core and capture responses coming out. In External mode, the core reconfigures the wrapper chains to launch values from the core outputs to test chip-level glue logic and interconnect while core inputs capture the responses. The wrapper chains, therefore, delineate between the logic tested in Internal mode and the logic tested in External mode.
In addition to the wrapper chains and clock control logic, it is also necessary to insert all scan chains, compression logic, memory BIST, logic BIST, IJTAG, and other control logic to make the core “DFT complete.” After the core is “DFT complete” it is possible to generate a set of scan patterns at the core level that can subsequently be retargeted to the chip level.
Creating “DFT Complete” cores results in a great deal of information about various DFT logic configurations, test modes (Internal and External), and test results such as patterns and fault data. The Tessent Shell Database (TSDB) enables all Tessent tools to use a unified flow, database, and user interface in order to track, store, and retrieve information necessary for integration and setup at each step, all the way to chip level. This flow significantly reduces the effort and risk of managing several error-prone tasks such as setting up the design for a specific mode of operation.
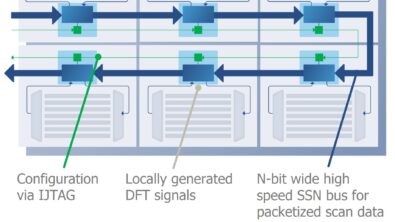
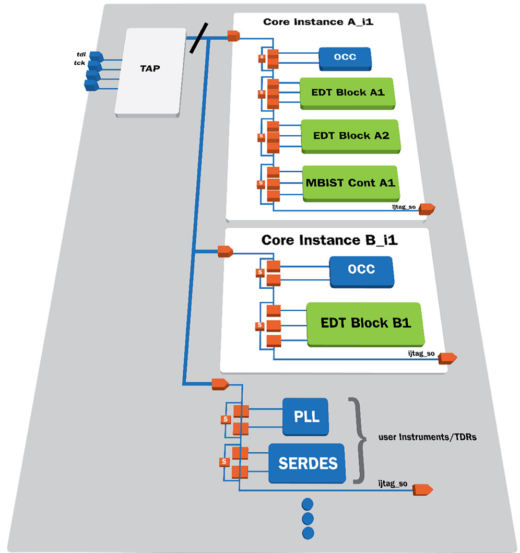 One of the key enabling technologies used in the Tessent flow is based on IJTAG. Typically, setting up the design for various test modes and at different levels of hierarchy is a very time-consuming and error-prone task. Using IJTAG, access to Tessent and other IEEE-compatible third-party IP is standardized through a common TAP controller. Higher level tool commands and procedures provide you with a simple interface for specifying the desired configuration while the tool manages the creation and tracking of all lower-level test cycles.
One of the key enabling technologies used in the Tessent flow is based on IJTAG. Typically, setting up the design for various test modes and at different levels of hierarchy is a very time-consuming and error-prone task. Using IJTAG, access to Tessent and other IEEE-compatible third-party IP is standardized through a common TAP controller. Higher level tool commands and procedures provide you with a simple interface for specifying the desired configuration while the tool manages the creation and tracking of all lower-level test cycles.
Employing the hierarchical test methodology has an incredible impact on SoC testing, including:
- ATPG, Verilog simulation, and diagnosis runtimes reduced by 5x-10x
- Memory footprint reduced by 5x-10x
- Scan pattern verification reduced by 5x-10x
- Pattern count reduction by as much as 2x
Learn all the details about the hierarchical DFT methodology and how you can reduce time and compute resources in our whitepaper here.