Protect Your Business with NextGen Access Controls
Achieve need to know access with Access Controls

The world has become a scary place today when it comes to data protection. Every day we hear about different digital data security threats, making it harder to ensure the protection of sensitive data in your PLM environment. Unfortunately, security threats can originate from people working inside the company. These “insiders” usually have authorized access to sensitive data and may know source: Federal Data Protection Report: 2018 how that information is protected, making it extremely hard to block the misuse of information while still allowing them to do their job. Under this situation, having strong access controls in place to achieve granular access control on user actions with “need to know access” to protect valuable intellectual property throughout the data lifecycle becomes a critical business need!

In view of these “insider” security threats, organizations are looking for revolutionary solutions that offer more granular access control on user actions. Ideally, these solutions could provide incremental access for user and admin activities, allow for simplicity in defining, managing, and analyzing security models, and provide organizations with the ability to strengthen their data access security.
Data security challenges

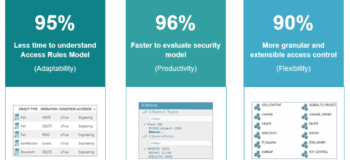
Siemens Teamcenter customers have communicated to us their need for higher data security. In Teamcenter 12.1 and Active Workspace 4.1, we introduced the NextGen Authorization Security solution called “Access Controls”. The Access Controls solutions offer simplicity in defining and managing security models with faster security model analysis, and granular access control on user actions with the flexibility to define access rule conditions. This is combined with easy administration in the Active Workspace client, all at a reduced total cost of ownership.
Why NextGen Authorization Architecture?

Many of our customers have told us about the new challenges they are facing in managing user access to data in Teamcenter. Their expectations for security include simple administration with an easy to use UI, simple rules to understand the security model, the ability to define and analyze security models faster, ease of extending access controls on user actions, flexibility to define access rule conditions without any codeful customizations, and so on.
Considering our customer expectations, and all of today’s security challenges mentioned in this article so far, we developed Teamcenter Access Controls. We built the new access management architecture based on six key guiding principles as shown here:
- Deny access protocol – by default, we ensure that the system denies user access, so you don’t need to write rules for denying user access. This way, the system ensures nobody has access unless an administrator grants it. Through this, it helps you to achieve “need to know access” and further strengthen data security with less number of rules.
- Simplified Access Rules Model – we have achieved this through the use of a flat list for granting access rules, where there is no precedence or order for access rule evaluation. This makes it much easier to understand the rule system, which has the feel of an excel sheet. You just need to focus on creating granting access rules, which will grant the user access to perform required actions on business objects and nothing else.

- Granular and Extensible Access Control – this we have ensured through the user action (aka operation in BMIDE) based access control, where you extend access control on any user action of your choice, including custom user actions. At the same time, we have eliminated the need for writing codeful customizations to write your own rule conditions using data and user attributes. This helps you to achieve granular and incremental access without having to give a user the “keys to the kingdom”.
- Faster Security Model Analysis – there are several methods to help you analyze and evaluate your security model faster. You can simply scan through the flat list of rules where you are equipped with search and filter options to identify rules based on operations (actions), conditions, business objects, and users, or use an automated test harness tool to define your test suite and automate its testing. At the same time, you can select objects in the active workspace client and use the access tab to understand who can perform what actions when in a particular role, group or project combination.
- Simplified Administration in Active Workspace Client – we have introduced rule administration in Active Workspace with an intuitive UI including search and filter support. This has simplified defining, managing and analyzing rules, conditions, and operation (user action) groups. When you administer rules through Active Workspace, those are applicable to all clients and all integrations, as the access evaluation happens on the server-side.

Protecting data from attacks posed by company “insiders” is a major issue for organizations today. The key problem companies need to solve is how to achieve granular access control with the need to know access, while still allowing insiders to do their jobs efficiently. Teamcenter Access Controls addresses this need most elegantly and is a big differentiator for Teamcenter. Access Controls saves you time and effort in achieving today’s data security business needs.
Stay tuned for my next post, where I will demonstrate the high value to your organization in using Teamcenter Access Controls to greatly reduce the burden of administrative tasks, and in turn – greatly reduce your security risks. I will take you through a deep dive into the new security solution, which has become much simpler and easier with Access Controls.


